Search results for tag #selfhosting
New post: IPv6 Foundations.
IPv6 isn't "the future of the internet." It's the internet. IPv4 is the relic we keep alive on NAT life support.
A laid-back tour through the basics: how the addresses are built, the two rules for crushing out the zeros, a /64 per subnet so you stop counting hosts, SLAAC, and why blocking ICMPv6 is a self-inflicted wound.
And no, dual-stack isn't a destination. It's a burden.
https://blog.hofstede.it/ipv6-foundations-the-internet-protocol-you-should-already-be-using/
Huh, looks like the new ASes, with LLM-bots attacking servers, just dropped 
TLDR: there are AS12876 and AS16276 — both located in France (Scaleway SAS and OVH SAS). My Asterisk self-hosted box was attacked from the next IPs: 62.4.15.81 and 51.222.38.229.
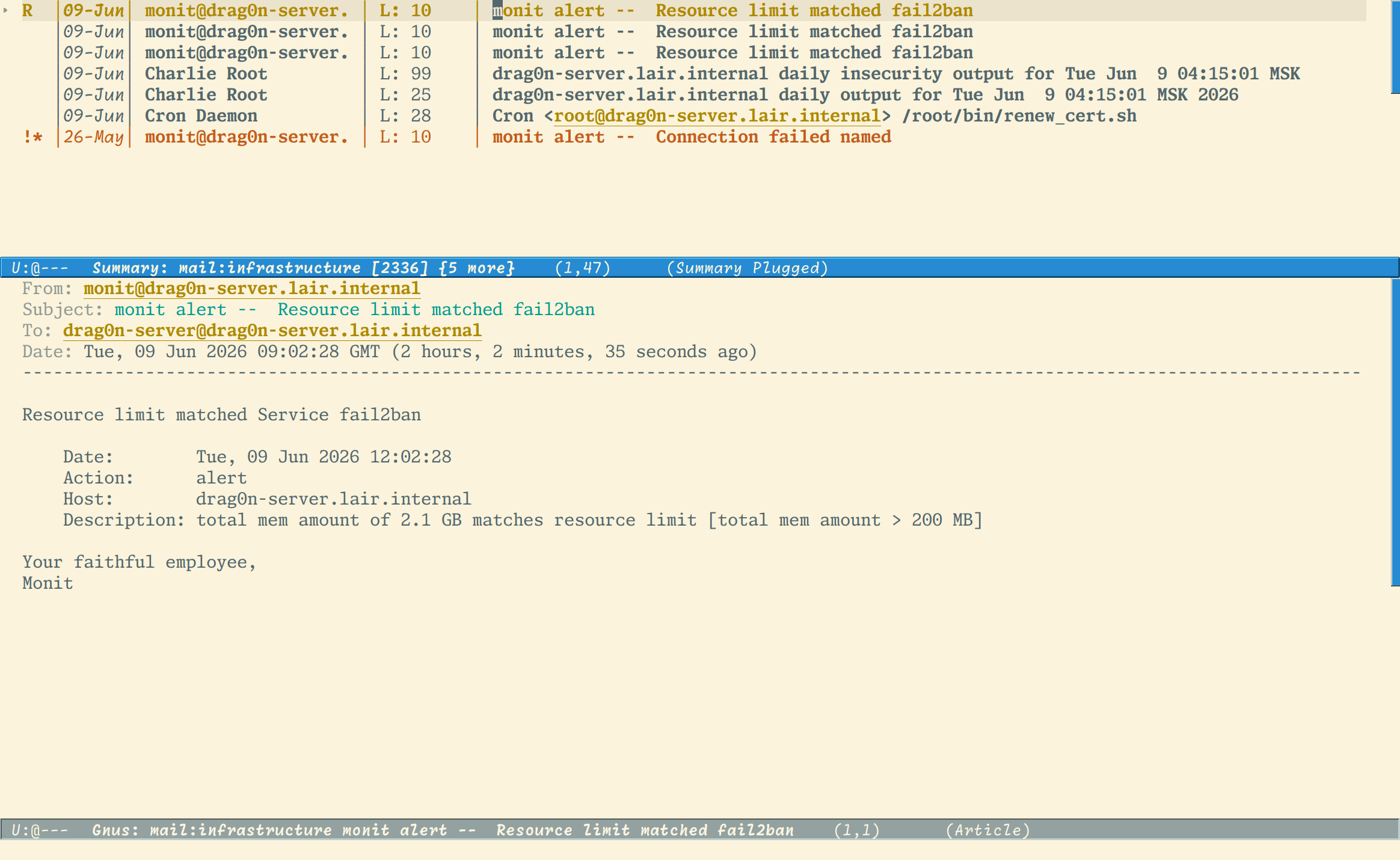
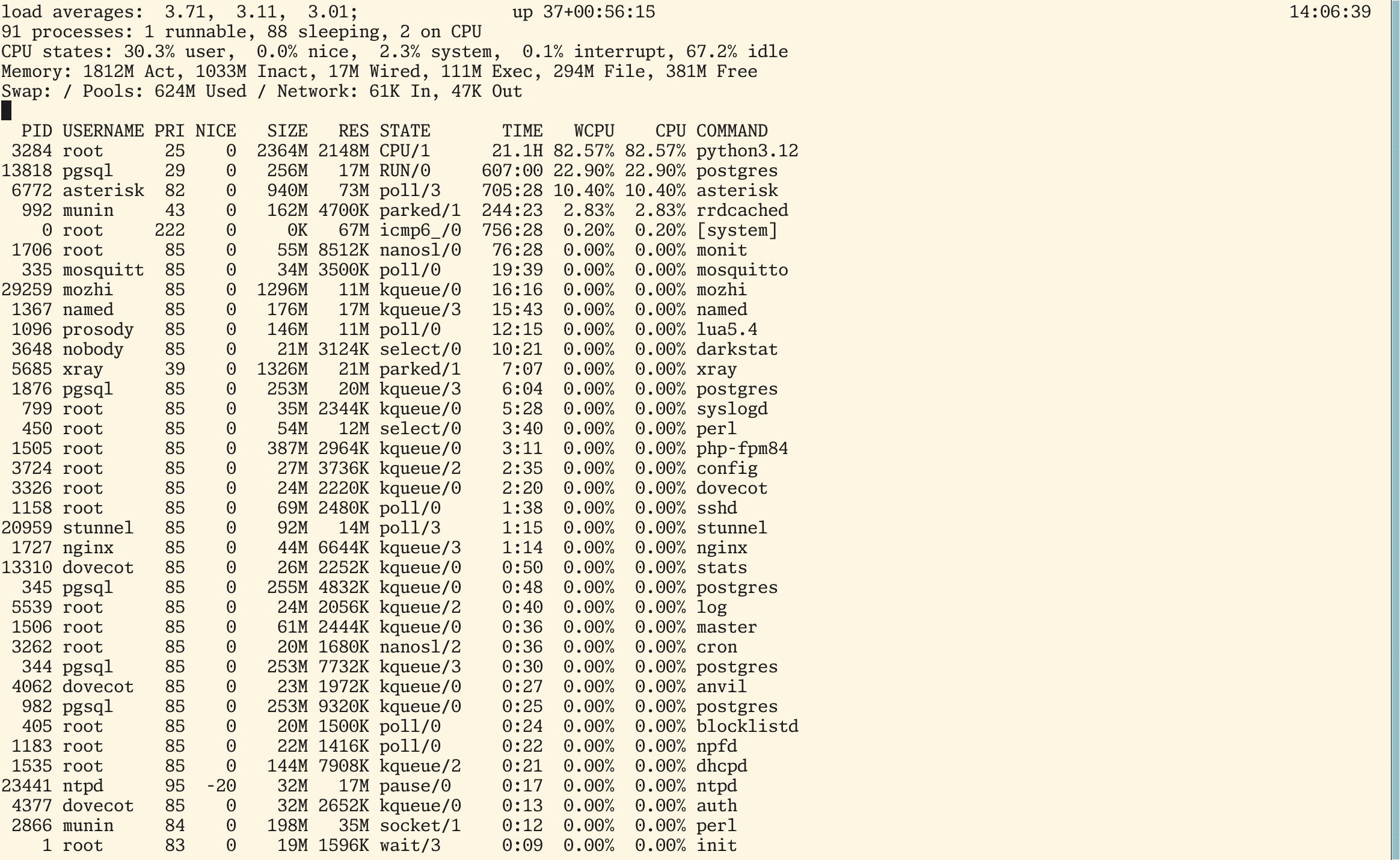
Today, after I was checked my e-mail, I found three warnings from Monit about fail2ban exhausting limits in my small server in the kitchen (Intel Atom N2800 1866 MHz and 4 Gb of RAM). First e-mail warns about fail2ban ate 200 MB of RAM, next about 500 MB of RAM and the last e-mail warns me that fail2ban ate 2 GB of RAM 
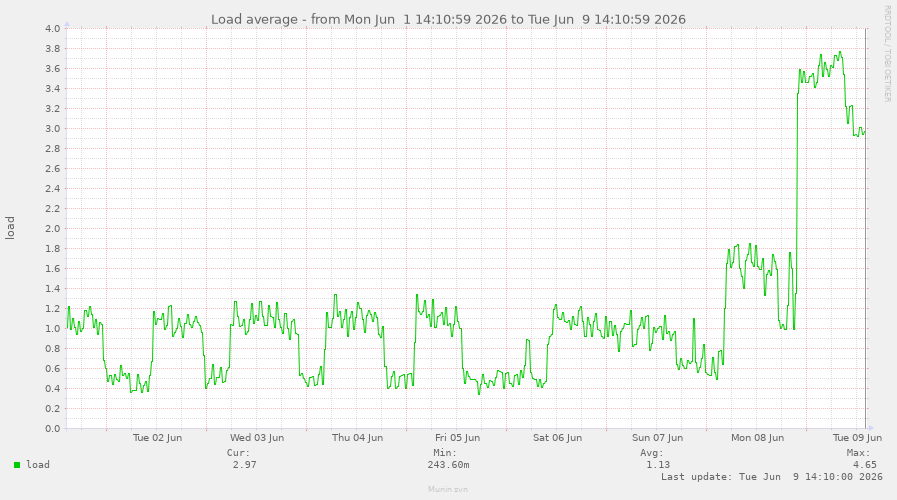
Then, I logged into my box and found that fail2ban, Asterisk and PostgreSQL aren't feeling well. The system load and the traffic amounts was unusual — the parameters are completely differs from which I used to see since server installation.
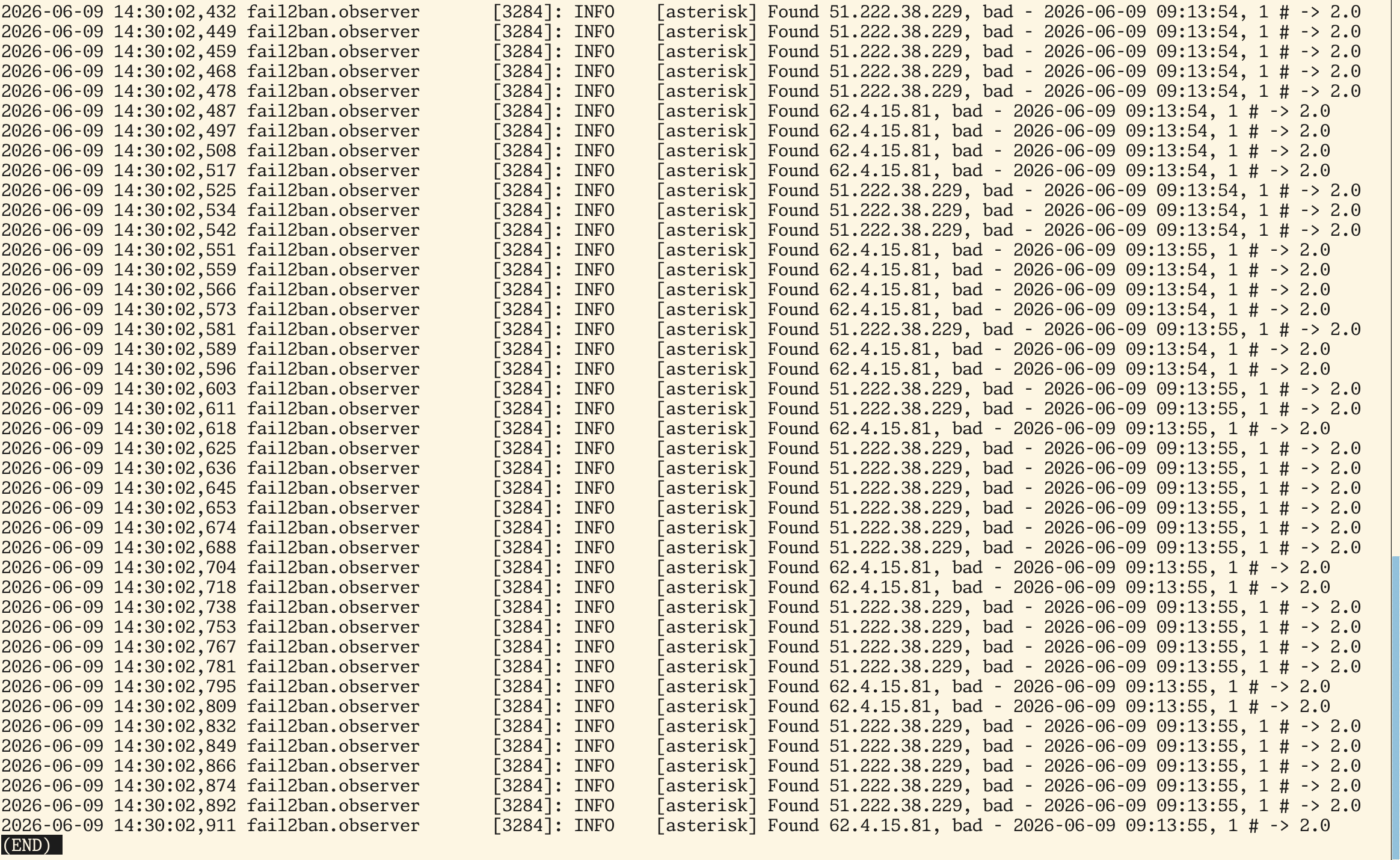
I checked fail2ban logs and found that it is still parses the data from Asterisk log which were happen at near 5 hours ago  And there were total mess in the Asterisk security.log (see screenshot) — some dumb (as it programmers
And there were total mess in the Asterisk security.log (see screenshot) — some dumb (as it programmers  ) LLM-bots were constantly trying to connect to my Asterisk server with HTTP protocol, evaluating it as a web-server, I dunno
) LLM-bots were constantly trying to connect to my Asterisk server with HTTP protocol, evaluating it as a web-server, I dunno 
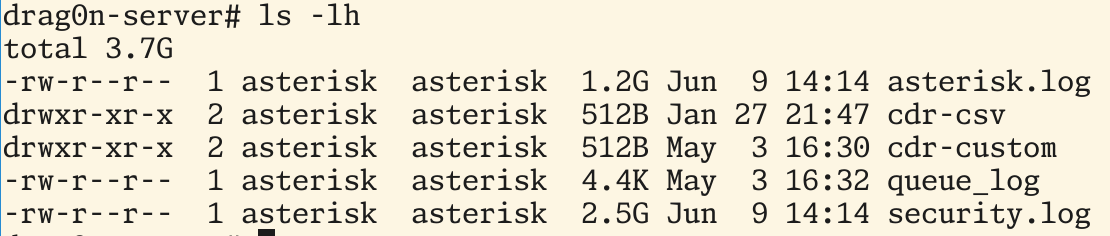
And the Asterisk logs became enormously big — while newsyslogd wasn't invoked — they eat at near 4 GB  . I didn't specify the maximal size of Asterisk logfiles in the /etc/newsyslog.conf, because I wasn't expected a lot of lines in the PBX logs, which is in use only for my relatives.
. I didn't specify the maximal size of Asterisk logfiles in the /etc/newsyslog.conf, because I wasn't expected a lot of lines in the PBX logs, which is in use only for my relatives.
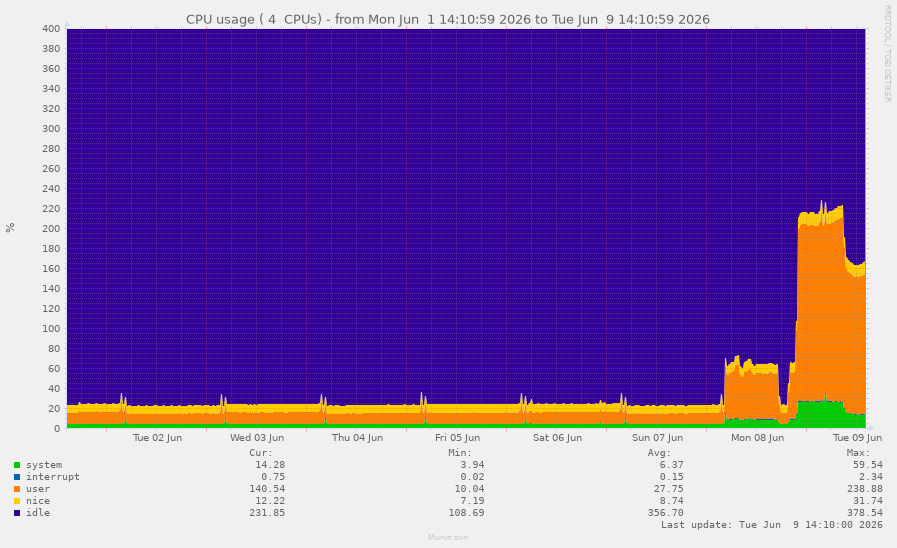
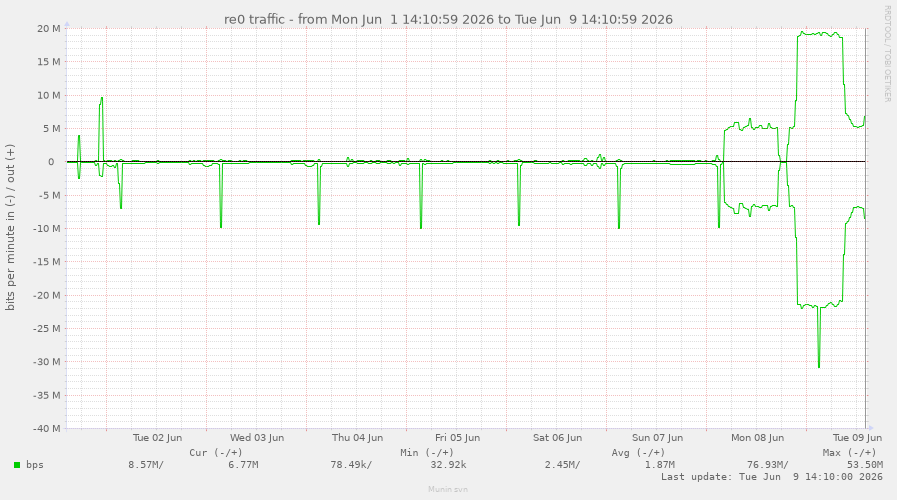
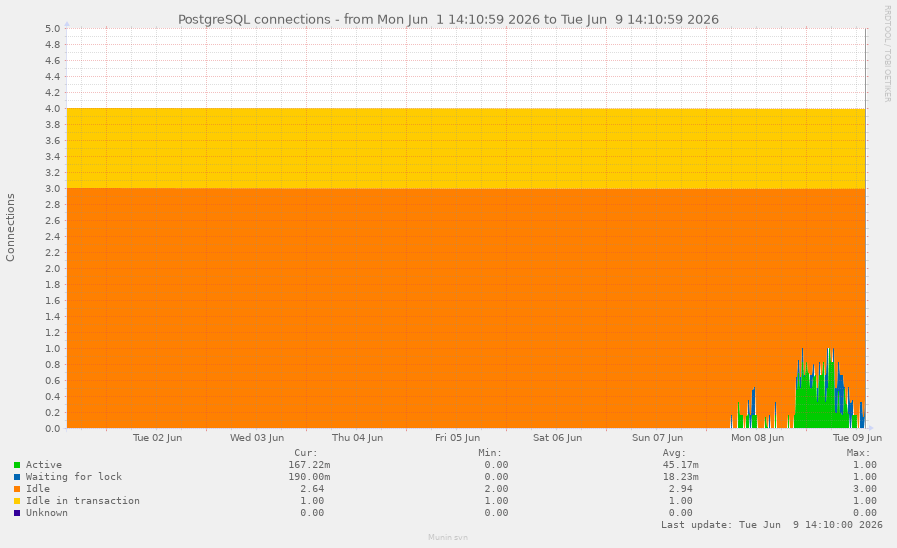
Some graphs  from #Munin with LLM-bots attacking my kitchen server.
from #Munin with LLM-bots attacking my kitchen server.
Graphs spans to the whole week, so on the left there is a normal state of my server. And on the right — attack is happening.
It's currently just a simplified version of my existing blog, but I'm hosting this website on my Raspberry Pi Zero for testing purposes:
We will see how things go over time, then possible port over the "real" thing 😛
Pondering a NAS rather than a usb drive attached to a raspberry pi or mini pc. Any recommendations for something reliable and not too expensive? If it can run Jellyfin & Nextcloud even better. Or at least be sensibly mounted for those services to use. #selfhosting #selfhosted #nas #nextcloud #jellyfin
We were without power for ~18 hours yesterday, but I’m still determined to eventually switch hosting my personal blog over to my local Raspberry Pi Zero
If you run your own local DNS servers at home, do you: (select all that apply)
Comment with your preferred DNS stack and privacy friendly DNS providers.
#FreeBSD #Linux #selfHosting #DNS
| Forward to ISP's DNS servers.: | 4 |
| Forward to a DNS service (1.1.1.1, 9.9.9.9, etc).: | 17 |
| Recursively resolve from root servers directly.: | 16 |
| Encrypt my DNS using DoH, DoT, etc.: | 14 |
I know "AI" is a polarizing topic around here, but I wanted to share a small side-project I've been tinkering with to scratch a personal itch: MastoSum.
It’s a lightweight web app that listens to public streams, filters for the hashtags I actually care about, and uses an LLM to generate a daily digest of the last 24 hours. Basically, a personalized news feed to help cut through the noise.
It works reasonably well for what I need. Here’s an example of today's run: https://mastosum.linuxserver.pro/s/6q1ZdTOuHBfKyQ3aVU3dOw
It's IPv6-only. Not reachable via IPv4.
#python #fastapi #mastodon #newsfeed #selfhosting #ai #llm #ipv6
@rastilin It'd be a good move to ditch GMail. I teach people how to go about it, and I'm thinking I should publish resources towards this end. But say the word if that's something that interests you. I want to see the world break free from GMail.
The outline: Buy a domain. Rent a VPS so you have an easy static IP address with reliable and power. Spin up BIND or similar. Serve up basic records for your domain. Make a glue record and delegate your domain to your name server using your registrar's web site. Next, spin up minimal web service and get a Let's Encrypt cert. Make a cron job to renew it. Spin up Postfix and Dovecot. Have Postfix use Dovecot auth and have them both use your Let's Encrypt cert. Add cron jobs to restart them when certs renew. Test. Now add MX and SPF records to your DNS. Consider spinning up DKIM, and adding records for that and DMARC to your domain. Consider procmail or maildrop for filtering and sorting. Consider RBLs, SpamAssassin, SpamProbe, and similar. Decide how you want to back the server up. Consider redundancy.
TFW you realize you've had your MX entry set wrong for over a month.
Yet somehow I've still been getting (some) mail? 🤔
Alright folks, it's time for me to zero in on my self-hosted RSS aggregator setup.
Priorities: ease of maintenance, support for a variety of readers (or at least Capy)
I know people have opinions. Tell me them!
Anybody have fun #irc channel and #xmpp MUC recommendations? Anything involving #sysadmin, #programming, #selfhosting and maybe fun nerdy #memes?
My experience with larger IRC channels on Libera have not been great. It'd be fun to find an online hangout.
Is there anyone out there running an AMD 5650GE based system running Linux or BSD?
Can you tell us your CPU and GPU idle power numbers as displayed in btop?
Maybe this is an "easy button" of sorts to reduce power on an existing AMD AM4 system without going through the machinations of new mobo, ram, etc., etc. Get most of the way there?
#Linux #RunBSD #AMD #5650GE #PowerConsumption #Power #HomeLab #SelfHosting #SelfHosted #SOHO
Is there anyone out there running an AMD 5825U based system running Linux or BSD?
Can you tell us your CPU and GPU idle power numbers as displayed in btop?
#Linux #RunBSD #AMD #5825U #PowerConsumption #Power #HomeLab #SelfHosting #SelfHosted #SOHO
Looks like it has basic Markdown -> HTML converting. Neat.
That
works
forme.
It also allows a subset of straight HTML.
- (I'm not gonna show it all)
It converts some text like
🙂into emoji, which I don't like, though. Leave my #emoticons alone ;)And of course, no post or poll length limit :)
I'm currently trying to wrap my head around setting up Radicle. The decentralization is kind of confusing when I'm used to centralized git hosting.
I have a selective seed node on my public-facing server, along with the radicle-httpd service which is reverse-proxied via Caddy. As I understand, this means I can seed (replicate) selected public repos to keep them in sync with the network. And the radicle-httpd service makes them available in an HTTP JSON API(?).
I also have a regular node on my workstation, with my dotfiles repository added to it for testing purposes.
I'm not sure how a regular node differs from a seed node. Do regular nodes also seed repositories like a seed node does, while a seed node's purpose is solely for seeding? If regular nodes also seed, is there still any reason to run a seed node separately?
I'd also like to get the radicle-explorer web UI set up on my public-facing server via reverse proxy. I'm not sure how that fits in with the rest of this. Does the radicle-explorer have to point to my seed node's HTTP endpoint to display the repositories I'm seeding?
I might have to go bother people in the Zullip chat.
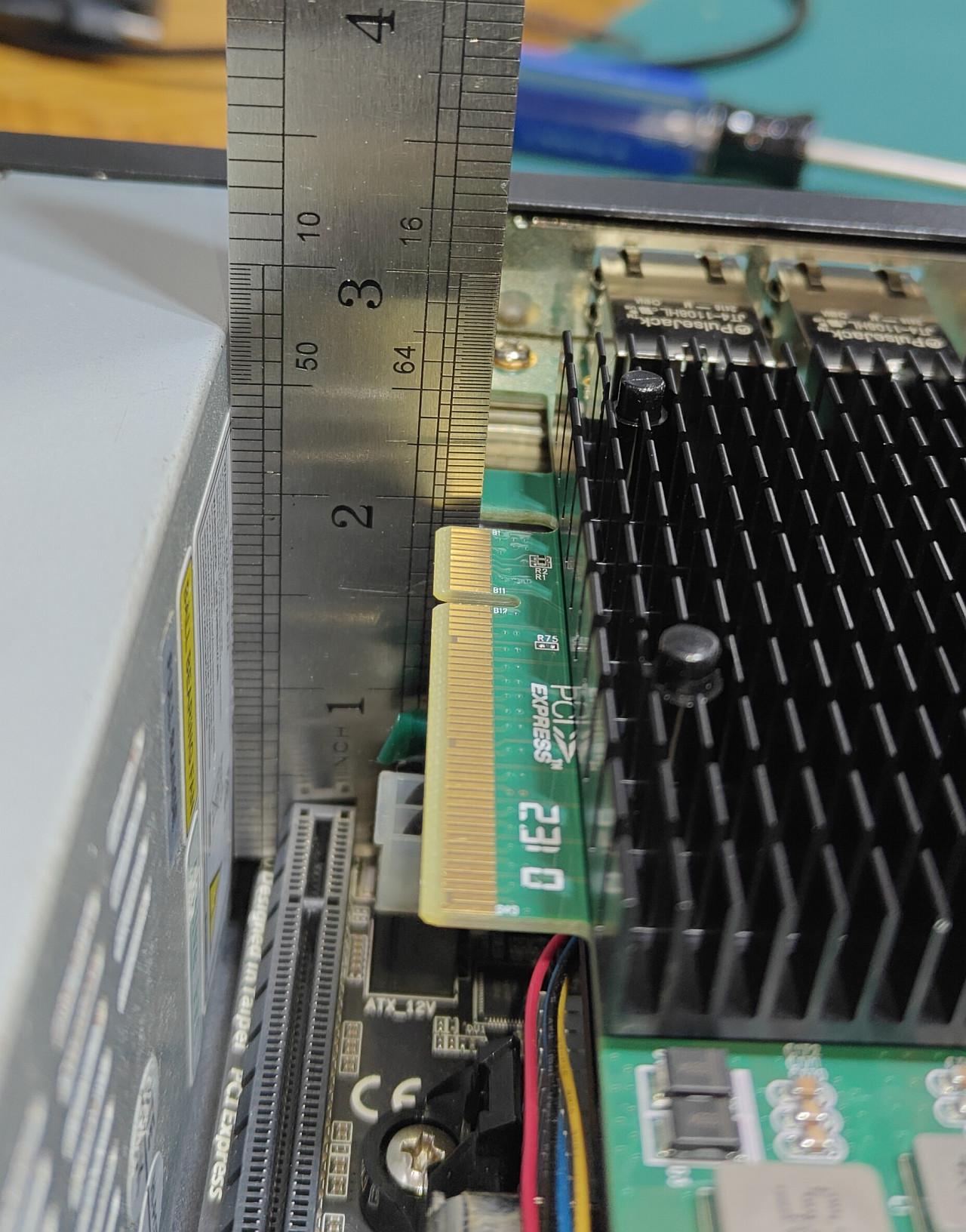
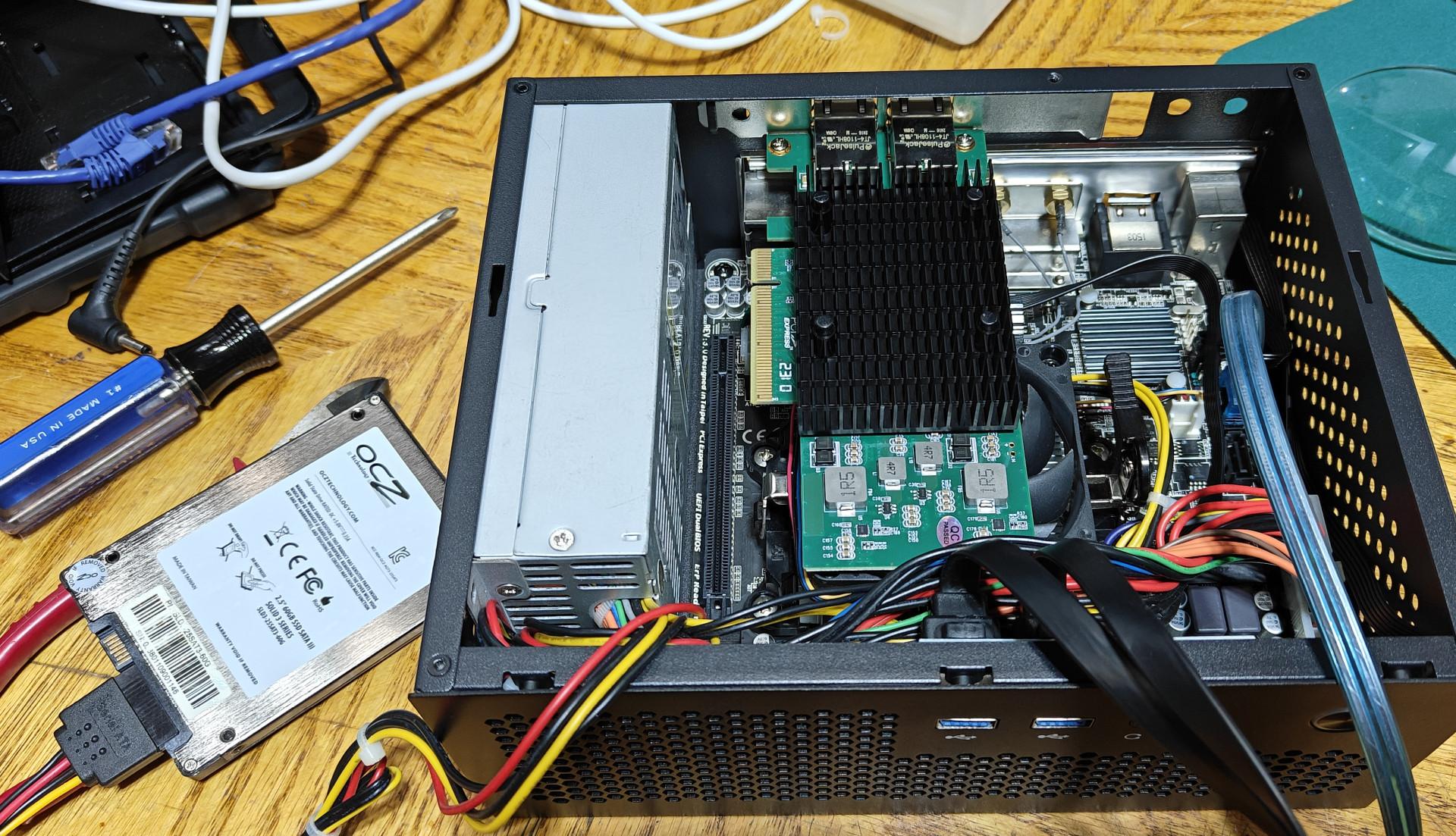
Almost done my custom recycled component OPNSense router. Final missing piece is this 2" PCIe riser. I may hit MicroCenter today. #opnsense #selfhosted #selfhosting #homekit

 boosted
boostedPleased to announce another edition of Cloudbreak, taking place May 28.
For those that don't know already, this is a 6hr fully-supported live training opportunity leading participants with no prior experience in system administration through the process of building up their own #sovereign & secured cloud server.
Hosted in the EU on renewable energy, the finished server also offers both Zoom & Google Docs alternatives.
Info & signup here:
Today in #selfhosting fun. I have a mail server that's been in place for years and hasn't had any noticable problems, but today I sent the same email from two different addresses to hotmail. Both had SPF, DKIM, DMARC and the same outbound IP address. One was delivered and one went to junk. Headers on the latter show a spam score of 5 (which is sufficient for it to be diverted):
X-MS-Exchange-Organization-SCL: 5
I tried running it through https://github.com/mgeeky/decode-spam-headers but that didn't give any clues
Hi folks! I would love to hear about the non-standard physical #homelab #selfhosting security measures you've taken. From alarms to boobytraps, from customized IKEA boxes to reinforced closets. The crazier the better!
One requirement: you need to have it implemented (at some point in the past or currently). No concepts that never left the design table please.
New #blogpost
I have come to share what I've done, some more confessions from a FOSS enthusiast...
https://joelchrono.xyz/blog/more-confessions-from-a-foss-enthusiast/
This is day 53 of #100DaysToOffload
What bring you to the path of self-hosting?
I guess for me is that because in the mid 2000's the free hosting services were quite terrible and I get my hands on the old family computer and some documentation about Debian.
 boosted
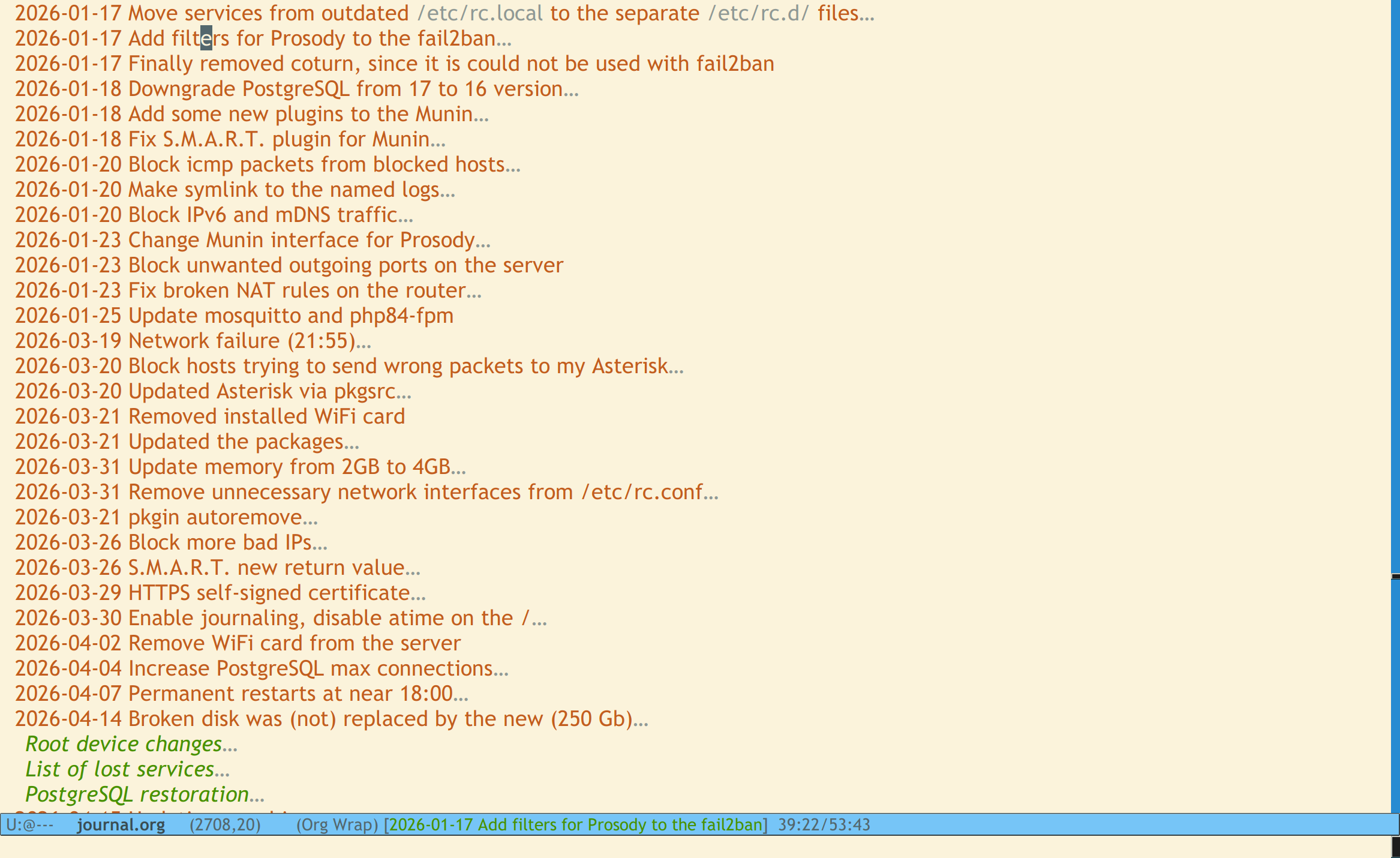
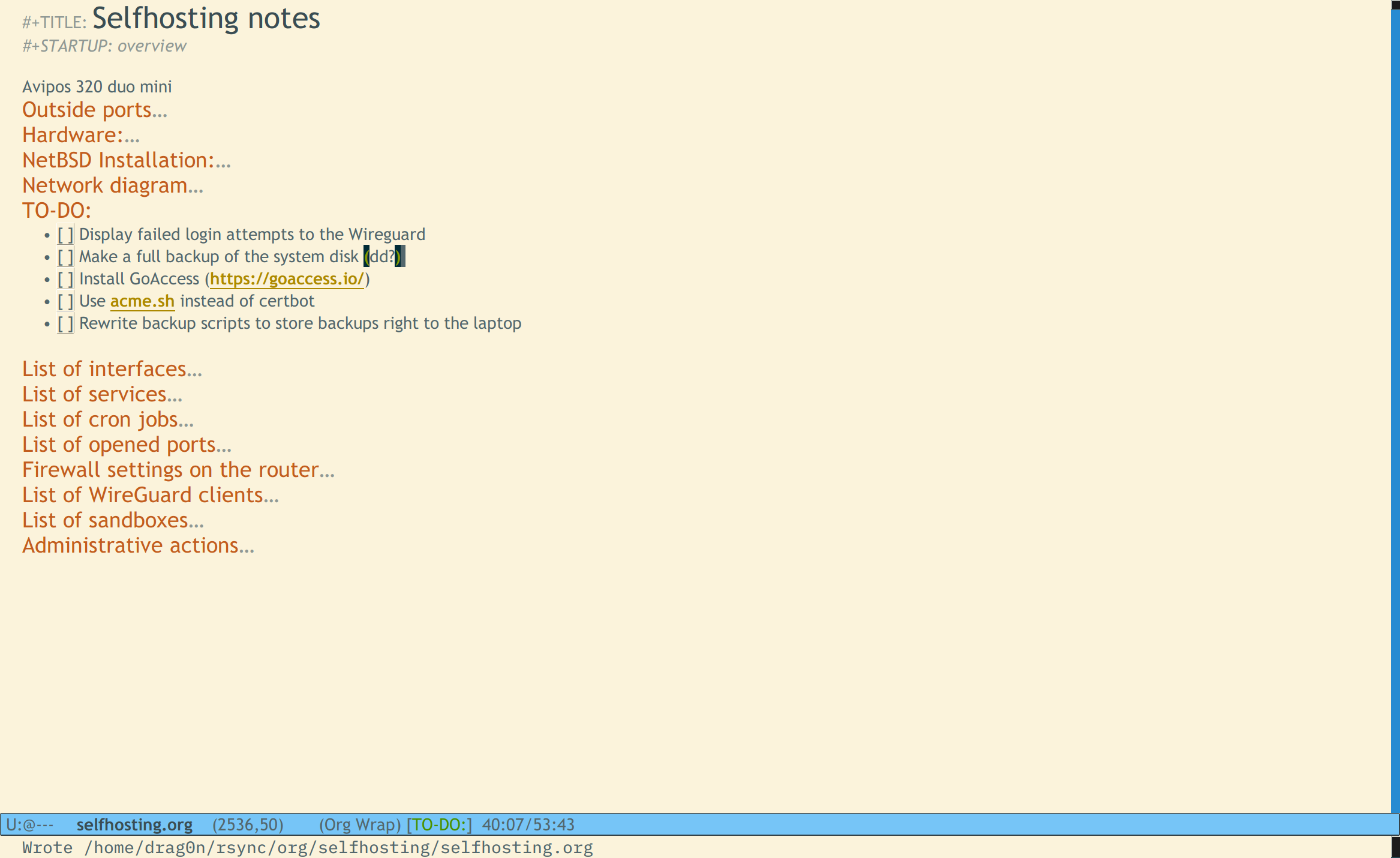
boostedLooks like not only backups but also my obsession^Wpassion to write detailed entries to my "selfhosting journal" pays back. Any change, I made in my main home server, has a date and a detailed description of changes made. Also, the process of #NetBSD installation and service installation is documented too, alongside with documented list of running services, opened ports, cronjobs, etc.
At one bad day, my main server started to hangup at near 18:00 and at nea 08:00. There weren't any cron (or any another) jobs at this time. In the logs and monitoring the problems with mosquitto (MQTT server) were visible — somehow it eats at near 100% of CPU, then monit restart it, then things become working, then (after some time) the server hangs completely. Investigation showed that write to my second ZFS disk (where the PostgreSQL DB lives) were extremely slowed, so ZFS panicked, crashed and crashes the kernel 
[ 204836.661198] wd0d: device timeout writing fsbn 123148477 of 123148477-123148478 (wd0 bn 123148477; cn 122171 tn 1 sn 46), xfer 38, retry 1
[ 204863.837664] wd0: soft error (corrected) xfer 38
[ 206810.672323] wd0: autoconfiguration error: wd_flushcache: status=0x5128<TIMEOU>
[ 212327.420695] SLOW IO: zio timestamp 211326864412007ns, delta 1000556283358ns, last io 211280726737075ns
[ 212327.420695] panic: I/O to pool 'zfs' appears to be hung on vdev guid 1299234741086050345 at '/dev/wd0'.
[ 212327.420695] cpu0: Begin traceback...
[ 212327.420695] vpanic() at netbsd:vpanic+0x183
[ 212327.420695] panic() at netbsd:panic+0x3c
[ 212327.420695] vdev_deadman() at zfs:vdev_deadman+0x15e
[ 212327.420695] vdev_deadman() at zfs:vdev_deadman+0x31
[ 212327.420695] spa_deadman_wq() at zfs:spa_deadman_wq+0xe0
[ 212327.430704] workqueue_worker() at netbsd:workqueue_worker+0xef
[ 212327.430704] cpu0: End traceback...
At the same time, I hear a strange metal noises from server at near 08:00 too, so the destiny of second drive was specified.
The server restoration will take some time, but since anything were written in the log file, I'm able just to replay some actions and get all systems up as soon as possible 
I've been running two degraded ZFS arrays for the last few weeks (Debian host).
Yeah, I know. Whatevs.
One of the pools was basically "scratch" backup space and one of the spindles died (breaking the utility of the mirror). Pulled the drive, wiped the remaining, put back in service with minimum fuss as a single drive. I'll throw another spindle at it when drive prices drop again.
The other array had the SSD cache die and it's been chugging along fine ever since. Not a big deal, but from a "experience" point of view it "feels slow" like a working md array.
New SSD arrived in the mail so that'll get sorted sometime today/tomorrow.
So, what's this post about?
Linux peeps, if you are thinking about md arrays, just stop, take the time, and throw 'yer leg over the zfs horse. It's worth it.
#Linux #RunBSD #zfs #md #mdadm #raid #homelab #SelfHosted #SelfHosting

 boosted
boostedNew post:
"A newbie's guide to self-hosting with #YunoHost. Part 5: Upgrades & Maintenance"
Not exactly the most exciting post I have ever written, but system maintenance is so essential.
And spoiler alert: thanks to a botched #PeerTube upgrade I discovered the wonders of #tmux (thank you @teapot_ben and @drfyzziks for recommending it!)


 [
[

![[?]](https://gts.tumfatig.net/fileserver/01FJ093H6Y5VGN20G998J7KN1M/attachment/original/01JZTJV1P9RVJ502PCXKN68R1F.jpeg)
 There is no Cloud!
There is no Cloud! Only someone else’s
Only someone else’s 
 [
[


 [
[